Since we work with many companies across industries, we have an opportunity to get an inside view of hundreds of accounting departments along with other operational areas, including IT. We see that with our clients, as with many other businesses, it can be really challenging to find time to improve the security of computing systems – there always seems to be something more urgent.
Here, we are sharing the story of one company's narrow escape and the decisions that came before and after it in hopes that you all will be encouraged to take at least one step – even a five-minute change – that could help protect your company's cash or your own. A few details have changed, but the story is true – just one example of the need for good IT and accounting practices.
We will call the company in question "Acme," a mid-size distributor with an email system and several financial systems, all in the cloud.
One day last year, the person responsible for Acme's accounts payable printed out a list of payments to be made and took them to his manager for approval.
As required by Acme's accounting processes, the manager made phone calls to double-check several of them since the amounts were large wires – over the amount that required additional verification.
Most of them checked out fine, but in one case, the manager said that she knew the vendor but wasn't sure what the payment was for and asked for more information.
As the Accounting Department followed up, they discovered that the bank information for the vendor had just been changed in the accounting system by the head of their Accounting Department, which seemed strange since that was not a task this person would usually do.
And sure enough, the head of the department knew nothing about it.
The company narrowly escaped losing $50,000 by wiring it to someone who had fraudulently redirected it to themselves – a potentially hefty "payday" for the scammer.
So how did this happen?
At this point, Acme's IT department got involved, and they discovered two things.
- First, the head of the Accounting Department had used the same password for both their email account and their accounting system account.
- Neither system used multi-factor authentication to require a code in addition to the password.
- Neither system used multi-factor authentication to require a code in addition to the password.
- Second, the person was told their accounting system password had minimal privileges (Primarily used for reporting), but this was not the case – the account actually had a very high level of permissions
There's a lot to be learned here.
Email Passwords
For one thing, we have all heard the advice never to duplicate passwords. That's technically best but also entirely impractical, given the 100 – 200 passwords most of us have - unless you use a password manager, a security step we strongly support. At the very least, you should never use email account passwords for any other accounts.
Why? Because once someone is in your email, they can not only impersonate you, but for many other kinds of systems, they can reset the password simply by requesting a password change link be sent to your email, which they now can see and control without your knowledge.
97 cents per thousand
The next problem is that there was no multi-factor authentication on the email or the accounting system, so once a password was stolen or guessed, the bad actor didn't need any other information to open the door and walk right in.
Do you think your passwords are clever and therefore safe? It is possible but unlikely. Here is a list of the 200 most common passwords used in 2021. The list details how many times a certain password was used and how long it would take to crack it.
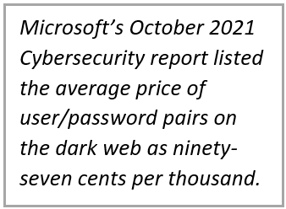 There are many passwords for sale, which are quite inexpensive. Microsoft's October 2021 Cybersecurity report listed the average price of user/password pairs on the dark web as ninety-seven cents per thousand. (If interested, the report says you can also pay $150.00 and get 400 million user/password pairs). Of course, not all these passwords are current, but it can take only a few – or maybe one – to open the door to a gold mine.
There are many passwords for sale, which are quite inexpensive. Microsoft's October 2021 Cybersecurity report listed the average price of user/password pairs on the dark web as ninety-seven cents per thousand. (If interested, the report says you can also pay $150.00 and get 400 million user/password pairs). Of course, not all these passwords are current, but it can take only a few – or maybe one – to open the door to a gold mine.
After purchase, the passwords are fed into software (malware-as-a-service) that allows them to be tested against and breach many systems, with zero technical knowledge required.
Account Permissions
Another issue raised is account permissions. When you have a password to high-value data such as banking information, health data, or credit cards (anything that can be sold or manipulated to end up with the cash), it is a good idea to ensure your access is correct. If you are a person who assigns this kind of account, it's a good idea to check twice to make sure the privileges are correct.
Acme’s story
At the end of the day, Acme escaped with no financial loss. They hired a security consultant and have now plugged all these holes and more, plus they have a plan to review and improve their security in the future. They escaped because of something that does not always get the attention it deserves – even though their computing security practices were not excellent at this point; their accounting processes were solid.
They required a human, not just software, to review certain kinds of payments (large ones, especially wires) and ensure they were legitimate. Even in our hyper-connected world, maybe especially here, there is sometimes no substitute for picking up the phone.

Learning security points I reviewed in this article might lead you to Google search more information. You will see thousands of articles, but before diving in, consider the source. Here are two resources we recommend, one for smaller to mid-sized businesses and one especially for nonprofits.
If this is of interest, download the whitepaper:
“10 Cybersecurity Tips for Small Businesses”
If you want help with your accounting department processes and want to ensure they are working in concert with your cybersecurity efforts, don't hesitate to contact us.
About the Author
Charlotte Morin is the IT Director for CFO Selections. She brings a unique combination of skills in technology, process development, and accounting to the CFO Selections team.
She joined the company in 2008, following six years as co-owner and controller of an e-commerce company, eleven years as a systems analyst, and three years working to build an internet company from the ground up.